Network Access Control
Network Access Control Lists allow you to restrict access to Monte Carlo's API, web application, and certain endpoints by IP address. When configured, only requests originating from IP addresses in the allowlist are permitted for the specified scope. This feature is managed via the GraphQL API using three operations: list, save (create or update), and delete.
Please note that this is different from the network controls and options used for data collection with most integrations, such as IP allowlisting, PrivateLink, and Agents/Data Stores.
See the networking documentation here for more details.
Scopes
Each Network Access Control List is associated with a scope that determines which endpoint it restricts. The following scopes are available:
| Category | Scope | Endpoint | Description |
|---|---|---|---|
| Agent | Agent | artemis.getmontecarlo.com | Restricts access to the Agent Service used by the Generic Agent |
| API | API | api.getmontecarlo.com | Restricts access to the Monte Carlo API |
| Airflow Callbacks | AirflowCallbacks | integrations.getmontecarlo.com/airflow/callbacks | Restricts access to the Airflow callback endpoint |
| Azure DevOps Webhook | AzureDevopsWebhook | integrations.getmontecarlo.com/gateway/azure-devops | Restricts access to the Azure DevOps webhook endpoint |
| Circuit Breaker | CircuitBreaker | integrations.getmontecarlo.com/checkpoint/circuit-breaker | Restricts access to the Circuit Breaker endpoint |
| Databricks Metadata | DatabricksMetadata | integrations.getmontecarlo.com/databrick/metadata | Restricts access to the Databricks metadata endpoint |
| Databricks Webhook | DatabricksWebhook | integrations.getmontecarlo.com/webhooks/databricks | Restricts access to the Databricks webhook endpoint |
| MCP | MCP | integrations.getmontecarlo.com/mcp/, mcp.getmontecarlo.com/mcp | |
| OpenTelemetry | OpenTelemetry | integrations.getmontecarlo.com/otel | Restricts access to the OpenTelemetry collector endpoint |
| Push Ingest API v1 | Ingestion | integrations.getmontecarlo.com/ingest/v1/ | Restricts access to the [Push Ingest APIs] endpoint |
| SCIM v2 | SCIM_v2 | integrations.getmontecarlo.com/scim/v2/ | Restricts access to the SCIM provisioning endpoint |
| UI | UI | Monte Carlo web application | Restricts access to the Monte Carlo web application based on source IP address |
| Global | Global | All of the above | Restricts all scopes listed above |
Network Access Control is supported on both global and regional endpoints
For example,
api.getmontecarlo.comandapi.eu1.getmontecarlo.com.
UI scope
The UI scope restricts access to the Monte Carlo web application based on the user's source IP address. When enabled, IP address validation is performed at login time and on subsequent requests. Users outside the allowlist will not be able to complete loading the application.
ImportantThe
UIscope does not preventgetmontecarlo.comfrom loading in the browser or block the login page from appearing. After a user authenticates, Monte Carlo validates the source IP address against the allowlist. If the address is not allowed, the application will not finish loading and the user will see an error message on the login page indicating that their IP address is not allowed.
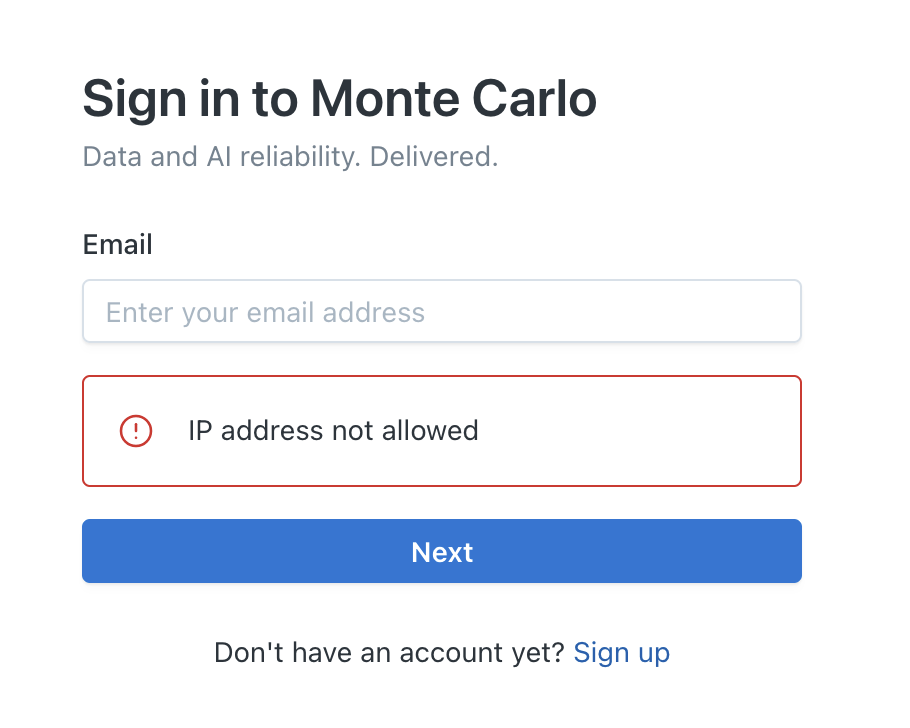
Error displayed when a user's IP address is not in the allowlist
Scope precedence
When a request is received, Monte Carlo first checks for a scope-specific access control list. If no scope-specific rule exists for that endpoint, it falls back to the Global configuration. This means a scope-specific rule takes precedence over the global rule.
Global scopeSetting a Network Access Control List on the
Globalscope restricts all endpoints listed above. If you set a global restriction, only IP addresses in the global allowlist will be able to access any scope that does not have its own scope-specific rule.
Usage
How Can I Use the API?
You can access the API through the API Explorer in the Monte Carlo UI. Learn more about the API Explorer here.
Alternatively, you can generate an API key and make API calls using tools such as cURL or Postman
Listing Network Access Control Lists
Use the getNetworkAccessControlLists query to retrieve all configured restrictions and their allowed IP addresses.
query GetNetworkAccessControlLists {
getNetworkAccessControlLists {
scope
allowedIps {
value
description
}
}
}{
"data": {
"getNetworkAccessControlLists": [
{
"scope": "api",
"allowedIps": [
{
"value": "203.0.113.10",
"description": "Office VPN"
},
{
"value": "198.51.100.0/24",
"description": "CI/CD pipeline"
}
]
}
]
}
}Creating or updating a restriction
Use the saveNetworkAccessControl mutation to create a new restriction or update an existing one for a given scope.
Replace behaviorThe
saveNetworkAccessControlmutation replaces the entire allowlist for the specified scope. If you want to add a new IP address to an existing list, you must include all previously allowed IP addresses in theallowedIpsarray along with the new one.
If you save a restriction on the
APIor an integration scope that excludes your current IP address, you can still log into the Monte Carlo web application and use the API Explorer to update or remove the restriction — unless theUIorGlobalscope also blocks your IP address.
mutation SaveNetworkAccessControl {
saveNetworkAccessControl(
scope: API
allowedIps: [
{ value: "203.0.113.10", description: "Office VPN" },
{ value: "198.51.100.0/24", description: "CI/CD pipeline" }
]
) {
saved
}
}{
"data": {
"saveNetworkAccessControl": {
"saved": true
}
}
}Parameters:
scope(required) — One of the scope values from the table above.allowedIps(required) — Array of IP address entries:value(required) — An IP address or CIDR range (e.g.,203.0.113.10or198.51.100.0/24).description(optional) — A human-readable label for the IP address entry.
Deleting a restriction
Use the deleteNetworkAccessControl mutation to remove the entire allowlist for a scope, restoring open access to that endpoint.
mutation DeleteNetworkAccessControl {
deleteNetworkAccessControl(scope: API) {
deleted
}
}{
"data": {
"deleteNetworkAccessControl": {
"deleted": true
}
}
}Parameters:
scope(required) — The scope to remove the restriction from.
Examples
Restricting API access to office IP addresses
To restrict API access so only your office network can make API calls:
Step 1: Save the restriction with your office IP addresses.
mutation SaveNetworkAccessControl {
saveNetworkAccessControl(
scope: API
allowedIps: [
{ value: "203.0.113.10", description: "Office - Main" },
{ value: "203.0.113.11", description: "Office - Backup" }
]
) {
saved
}
}Step 2: Verify the restriction is in place.
query GetNetworkAccessControlLists {
getNetworkAccessControlLists {
scope
allowedIps {
value
description
}
}
}Restricting a single integration
To restrict only the Circuit Breaker endpoint to requests from a specific Airflow instance:
mutation SaveNetworkAccessControl {
saveNetworkAccessControl(
scope: CircuitBreaker
allowedIps: [
{ value: "10.0.1.50", description: "Airflow production instance" }
]
) {
saved
}
}This does not affect access to other endpoints like the API or other integrations.
Restricting UI access to corporate network
To restrict Monte Carlo web application access to your corporate network:
mutation SaveNetworkAccessControl {
saveNetworkAccessControl(
scope: UI
allowedIps: [
{ value: "203.0.113.0/24", description: "Corporate network" },
{ value: "198.51.100.0/24", description: "VPN egress" }
]
) {
saved
}
}Users outside these IP address ranges will still see the Monte Carlo login page, but after authenticating, the application will not finish loading and they will see an error message indicating their IP address is not allowed.
Setting a global restriction
To restrict all endpoints at once using the Global scope:
mutation SaveNetworkAccessControl {
saveNetworkAccessControl(
scope: Global
allowedIps: [
{ value: "203.0.113.0/24", description: "Corporate network" }
]
) {
saved
}
}With this in place, any scope that does not have its own scope-specific rule will only accept requests from the corporate network. If you later add a scope-specific rule (e.g., for CircuitBreaker), that scope will use its own allowlist instead of the global one.
To remove the global restriction:
mutation DeleteNetworkAccessControl {
deleteNetworkAccessControl(scope: Global) {
deleted
}
}FAQs
Are controls on a per–Monte Carlo account (workspace) basis?
Yes. Controls are applied per Monte Carlo account (workspace). If you have multiple accounts, you can manage controls independently for each one.
How long does it take for changes to apply?
Updates to allowlists typically take effect within a few minutes, generally within 5 minutes. In some cases, propagation may take slightly longer due to caching or network distribution delays.
What is the behavior if there are no network rules or access controls set?
If no IP addresses are explicitly allowlisted, access is permitted from any IP address.
Authentication (for example, token verification) is still always enforced, and all traffic is transmitted over HTTPS
What IP address format is supported?
Both individual IP addresses (e.g., 203.0.113.10) and CIDR notation (e.g., 198.51.100.0/24) are supported.
What happens if I set a restriction that excludes my current IP address?
If the restriction is on the API or an integration scope, you will not be fully locked out — you can still log into the Monte Carlo web application and use the API Explorer to update or remove the restriction.
If the restriction is on the UI or Global scope and excludes your IP address, you will not be able to use the web application. In this case, you would need to use the Monte Carlo CLI or direct API calls from an allowed IP address to update or remove the restriction.
How does the global scope interact with scope-specific restrictions?
Monte Carlo checks for a scope-specific rule first. If one exists, it is used. If no scope-specific rule is found, the global rule is checked. This means scope-specific rules take precedence over the global rule.
The Global scope is used as a fallback when no scope-specific rule exists.
Does this affect the Monte Carlo UI?
Yes, when the UI scope (or Global scope) is configured. The UI scope validates the user's source IP address at login time and on subsequent requests. Users outside the allowlist will see the login page but will not be able to complete loading the application after authenticating — an error message will be displayed indicating that their IP address is not allowed.
Other scopes (API, integration-specific scopes) do not affect the web application UI.
Alternatively, you can restrict UI access by configuring IP address restrictions directly in your SSO identity provider.
How do I add a new IP address to an existing restriction without removing the old ones?
First, query the current list using getNetworkAccessControlLists to get all existing IP addresses for the scope. Then call saveNetworkAccessControl with the full list of IP addresses (existing plus new). The save operation replaces the entire list, so you must include all IP addresses you want to keep.
API Documentation
Detailed documentation for these operations is available in our API documentation:
Updated about 1 month ago
