MCP Server
How AI agents interact with Monte Carlo
Overview
The Monte Carlo MCP Server provides AI agents and assistants with direct access to Monte Carlo's data observability platform through the Model Context Protocol (MCP). This integration enables seamless interaction with Monte Carlo's monitoring, alerting, and data quality capabilities directly from supported AI environments like Cursor, Claude Desktop, and Visual Studio Code.
Want smarter agents, not just connected ones? The MCP Server gives your AI agent access to Monte Carlo's tools. The Agent Toolkit goes further — it teaches your agent how to use those tools effectively, with pre-built skills for monitoring, code change validations and more. Get started with the Agent Toolkit →
How to set up
1. Connect to the MCP Server
There are two ways to authenticate with the Monte Carlo MCP Server: using MCP Server keys (manual credential setup) or OAuth 2.1 (browser-based login). Both methods require the same permissions — only users with roles that can create MCP integration keys (Editors, Monitor Editors, Domain Managers, and Account Owners) are able to authenticate.
Option 1: OAuth 2.1 (recommended for MCP clients that support HTTP transport)
MCP clients that support HTTP-based transport can connect using OAuth 2.1, which lets you authenticate through the Monte Carlo website — no API keys to manage.
Setup in Claude Code
Run the following command to add the Monte Carlo MCP server:
claude mcp add --transport http monte-carlo-mcp https://mcp.getmontecarlo.com/mcpThe next time Claude Code attempts to use the MCP server, your browser will open to the Monte Carlo login page. After signing in, you will see a consent screen asking you to authorize access:
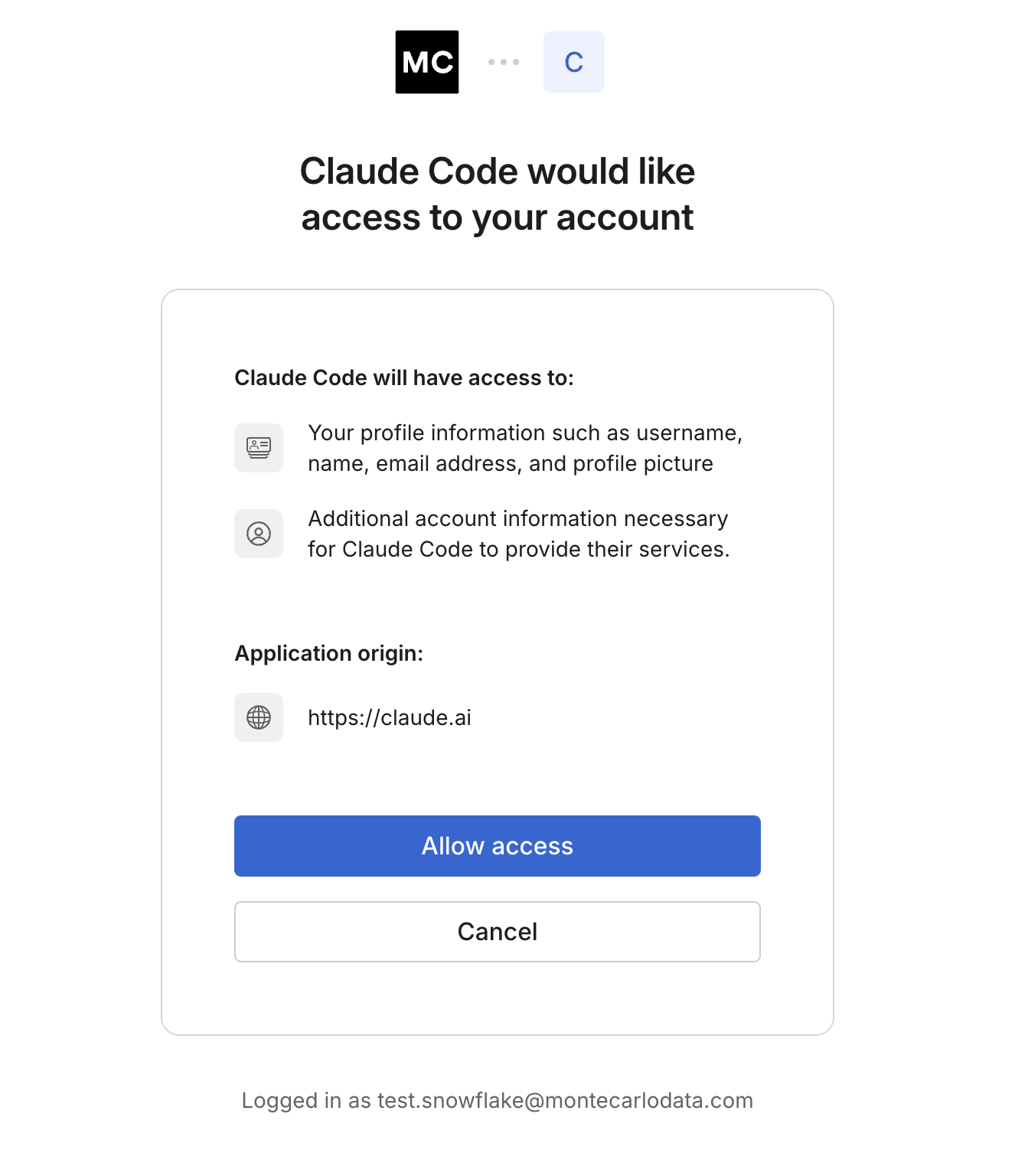
Click Allow access to complete the connection. Claude Code will now be able to interact with your Monte Carlo account.
Setup in Cursor
In your mcp.json, add the Monte Carlo server with just the URL — no keys needed:
{
"mcpServers": {
"monte-carlo": {
"url": "https://mcp.getmontecarlo.com/mcp"
}
}
}When Cursor connects to the server, your browser will open to complete authentication.
Setup in Visual Studio Code
Open your MCP configuration (MCP: Open User Configuration) and add:
{
"servers": {
"monte-carlo": {
"url": "https://mcp.getmontecarlo.com/mcp"
}
}
}When VS Code connects to the server, your browser will open to complete authentication.
Setup in other MCP clients
Any MCP client that supports HTTP transport with OAuth 2.1 can connect to the Monte Carlo MCP Server using the endpoint:
https://mcp.getmontecarlo.com/mcpConfigure your client to use HTTP transport with the URL above. On first connection, the client will initiate the OAuth flow and redirect you to the Monte Carlo website for authentication and consent.
Option 2: MCP Server keys (works with all MCP clients)
If your MCP client does not support HTTP transport or OAuth, you can use MCP Server keys instead.
Prerequisites
- Cursor Version: 1.7.17+ (if you use Cursor)
- VSCode Version: 1.99.3+ (if you use VS Code)
- Claude Desktop Version: 0.13.19+ (if you use Claude)
- Node.js (LTS) + npm installed (this includes
npx) - Network access to your Monte Carlo MCP endpoint (prod or dev).
- Your Key id and Key secret ready.
- MC Cli v0.141.4+ (if you want to create the MCP Server keys using the Cli)
Once you have your Key id and Key secret, add the Monte Carlo MCP Server to your IDE.
Monte Carlo's MCP Server should work for all LLM apps that support MCP. Below are the specific installation instruction for the common LLM applications.
Create MCP Server keys
First, you will need to create MCP server keys for authenticating into your own Monte Carlo API access. Note that MCP Server keys are scoped credentials that grant access only to the Monte Carlo MCP Server. They are not the same as standard API keys, and API keys will not work with the MCP Server. Only users with roles: Editors, Monitor Editors, Domain Managers and Account Owners will be able to create MCP Server keys (same as for API keys).
Why separate keys for MCP server?
- Least privilege: MCP keys can’t be reused against other Monte Carlo APIs.
- Operational clarity: Easier to rotate/revoke without affecting other integrations.
Security tips: Treat the Key secret like any other credential. Store it securely (e.g., a secrets manager, 1Password, etc). If it’s lost or exposed, create a new key and revoke the old one.
You can create MCP Server keys via the UI, the CLI, or the GraphQL API.
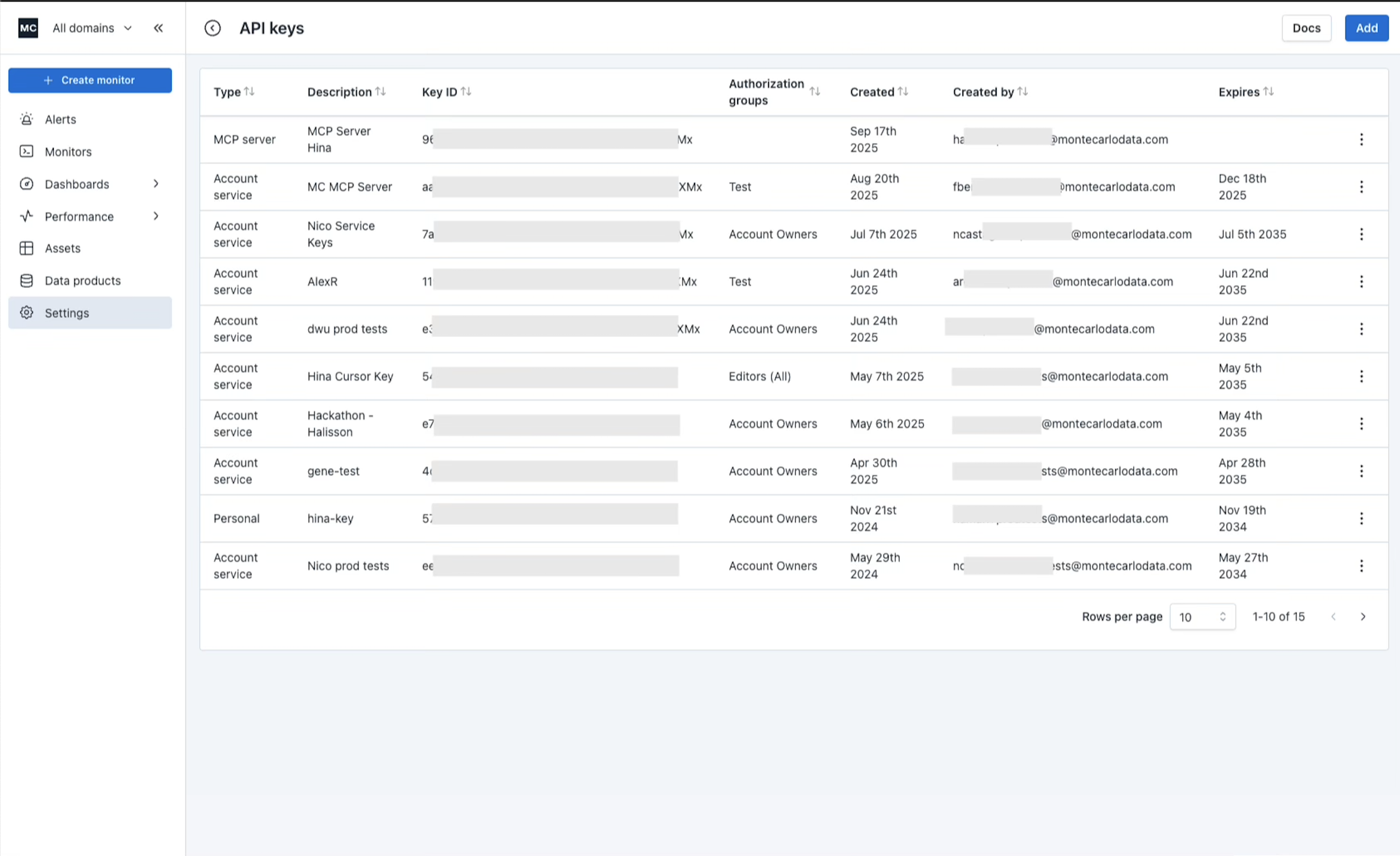
Option A: via UI
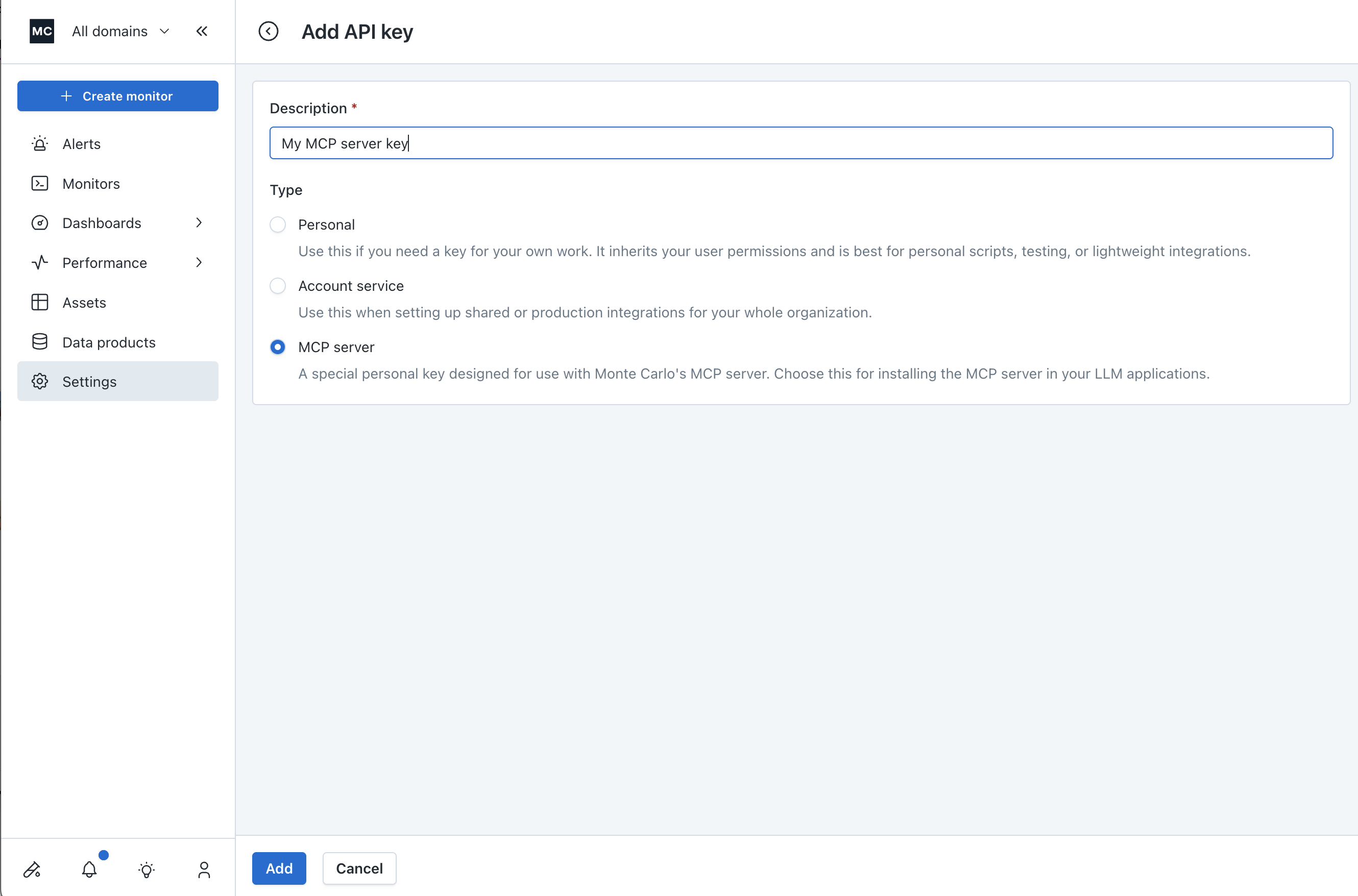
Go to Settings -> API Keys in the Monte Carlo UI, click on the blue "Add" button to start creating a MCP server key.
Select "MCP server" as the API key type, add a description to the key, then hit "Add".
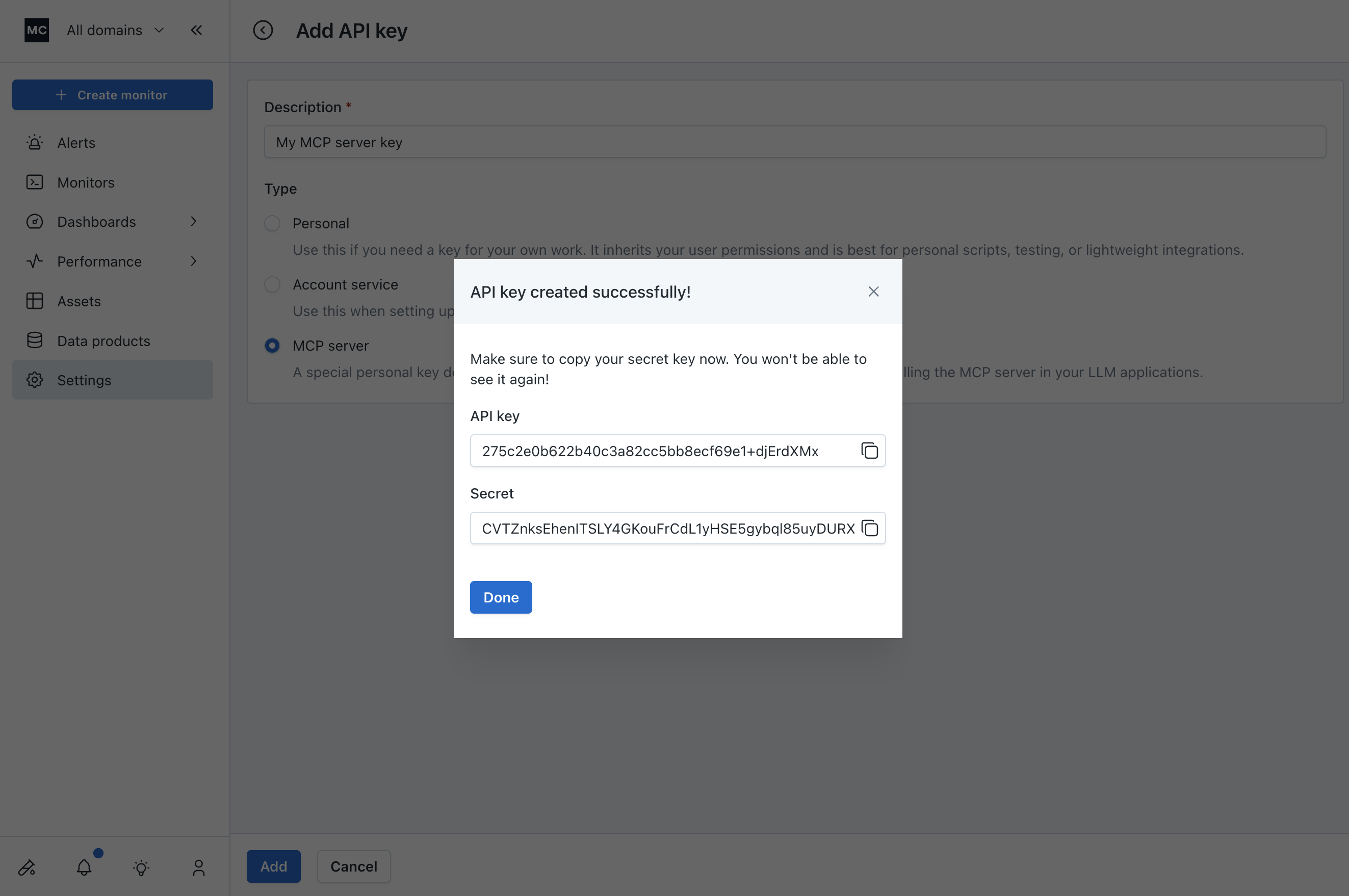
Copy your API key and secret. You will use these to install the MCP server in your LLM app.
Option B: via CLI
Prerequisite: You’re logged in to the Monte Carlo CLI with permissions to create integration keys.
montecarlo mcp create-key --description "Local test key"The command returns a Key id and Key secret:
Key id: XXX
Key secret: YYYCopy both values and store them securely.
Option C: via GraphQL API
Use the createMcpIntegrationKey mutation:
mutation CreateMcpIntegrationKey($description: String) {
createMcpIntegrationKey(description: $description) {
key {
id
secret
}
}
}Variables:
{
"description": "Local test key"
}Notes:
- The response includes both
idandsecret. Store them securely.
Setup in Cursor
- Open Cursor → Settings.
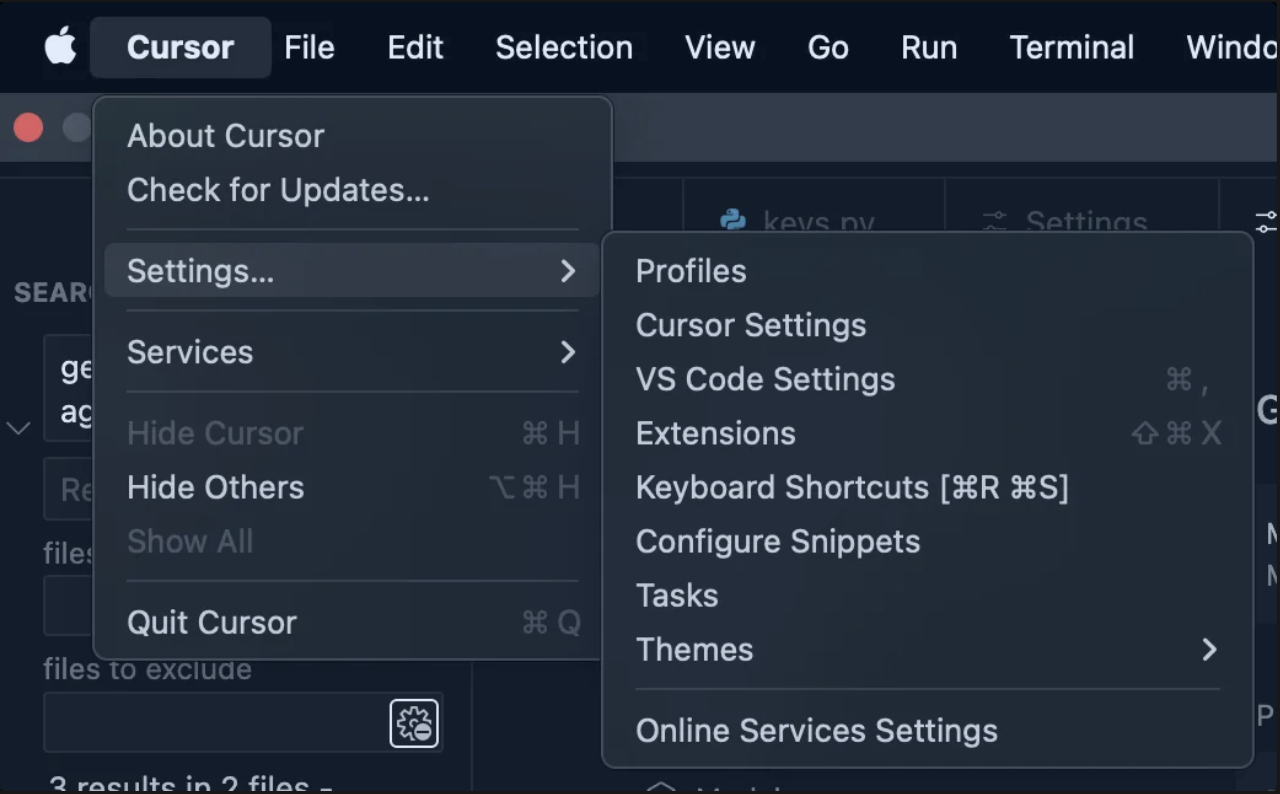
- Select MCP & Integrations.
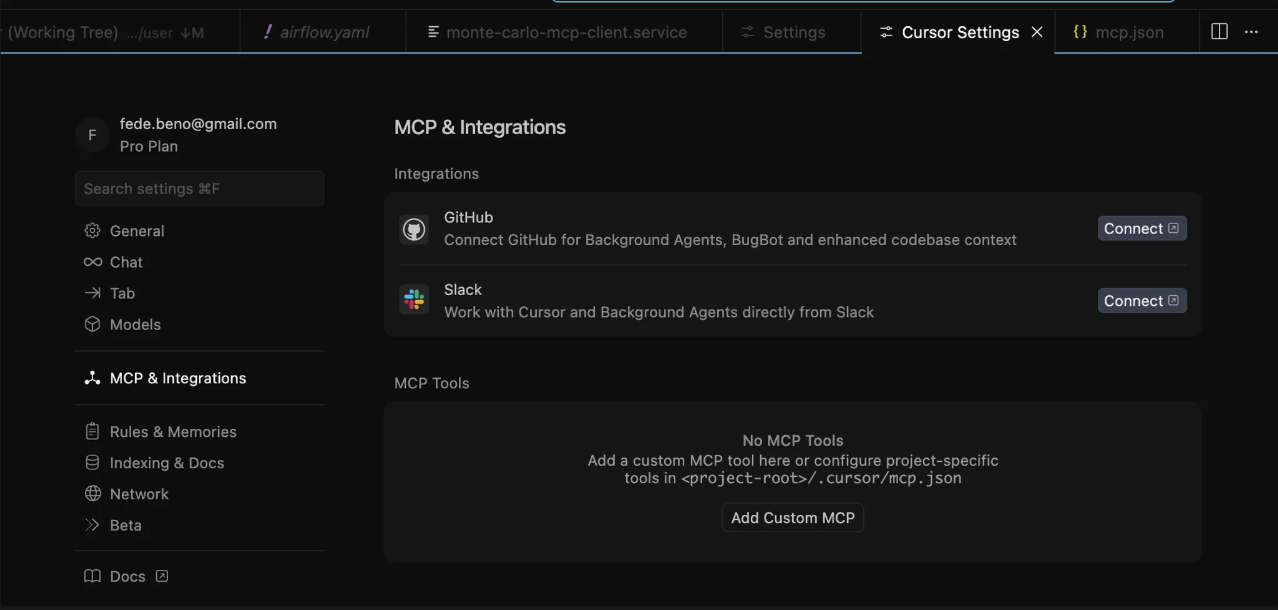
- Click Add Custom MCP. Cursor will open your
mcp.json. If you have no MCPs yet, it looks like:
{
"mcpServers": {
}
}- Add the Monte Carlo entry inside
mcpServers(replace<KEY_ID>and<KEY_SECRET>with your values obtained from the previous step. The URL should be:https://mcp.getmontecarlo.com/mcp/):
{
"mcpServers": {
"monte-carlo": {
"command": "npx",
"args": [
"-y",
"mcp-remote",
"https://mcp.getmontecarlo.com/mcp/",
"--header",
"Authorization: Bearer <Key Id>:<Key Secret>"
]
}
}
}Alternatively, we also support using custom headers instead of Authorization, so you can use the following:
{
"mcpServers": {
"monte-carlo": {
"command": "npx",
"args": [
"-y",
"mcp-remote",
"https://mcp.getmontecarlo.com/mcp/",
"--header",
"x-mcd-id: <KEY_ID>",
"--header",
"x-mcd-token: <KEY_SECRET>"
]
}
}
}- Save
mcp.jsonand return to Settings → MCP & Integrations. You should see a monte-carlo toggle.
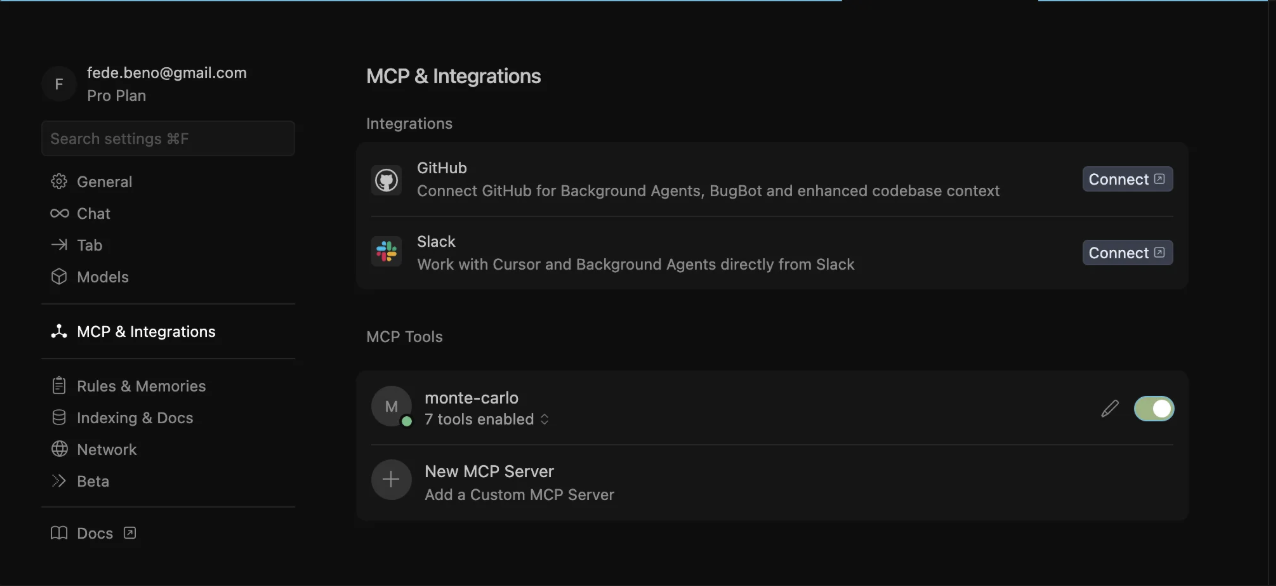
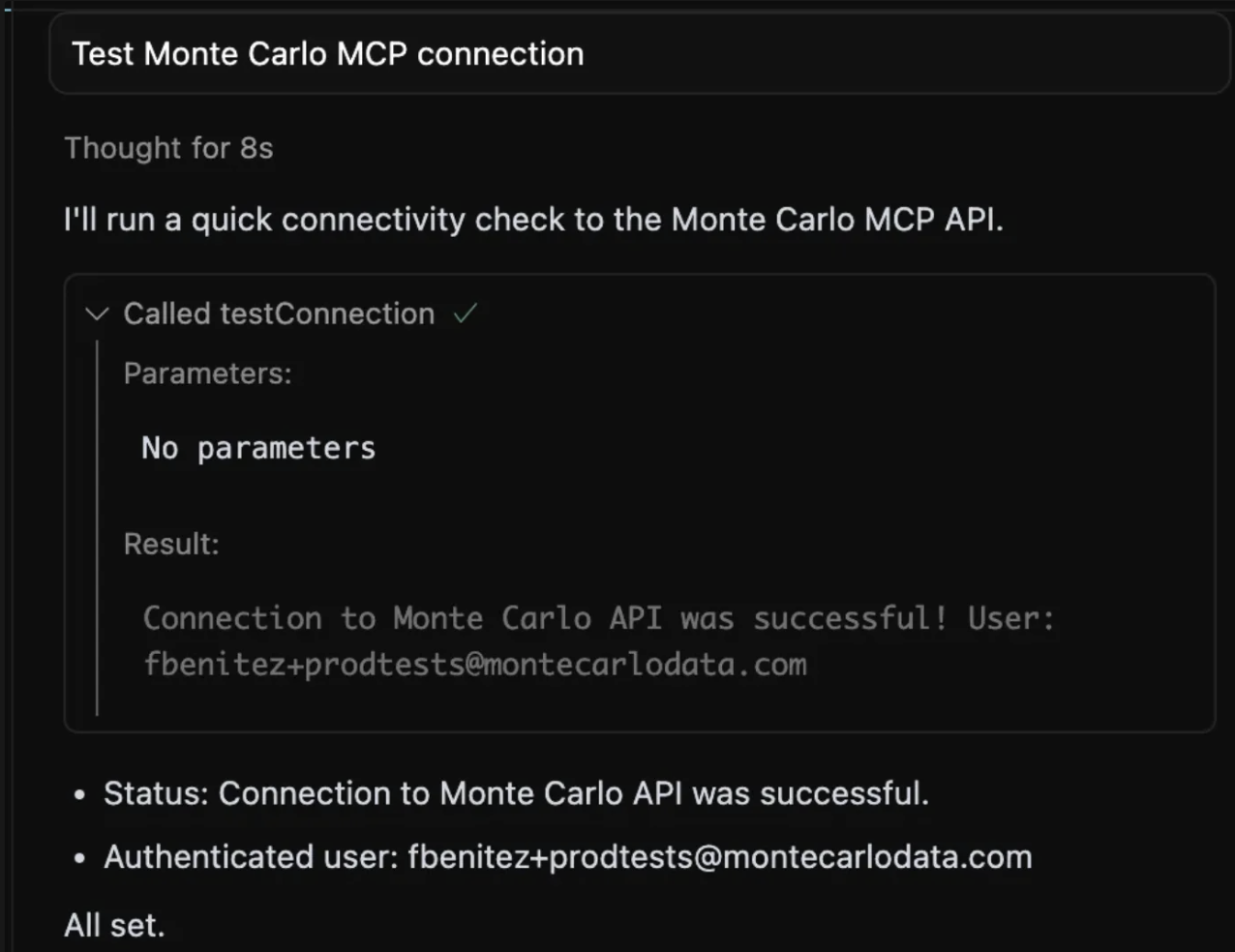
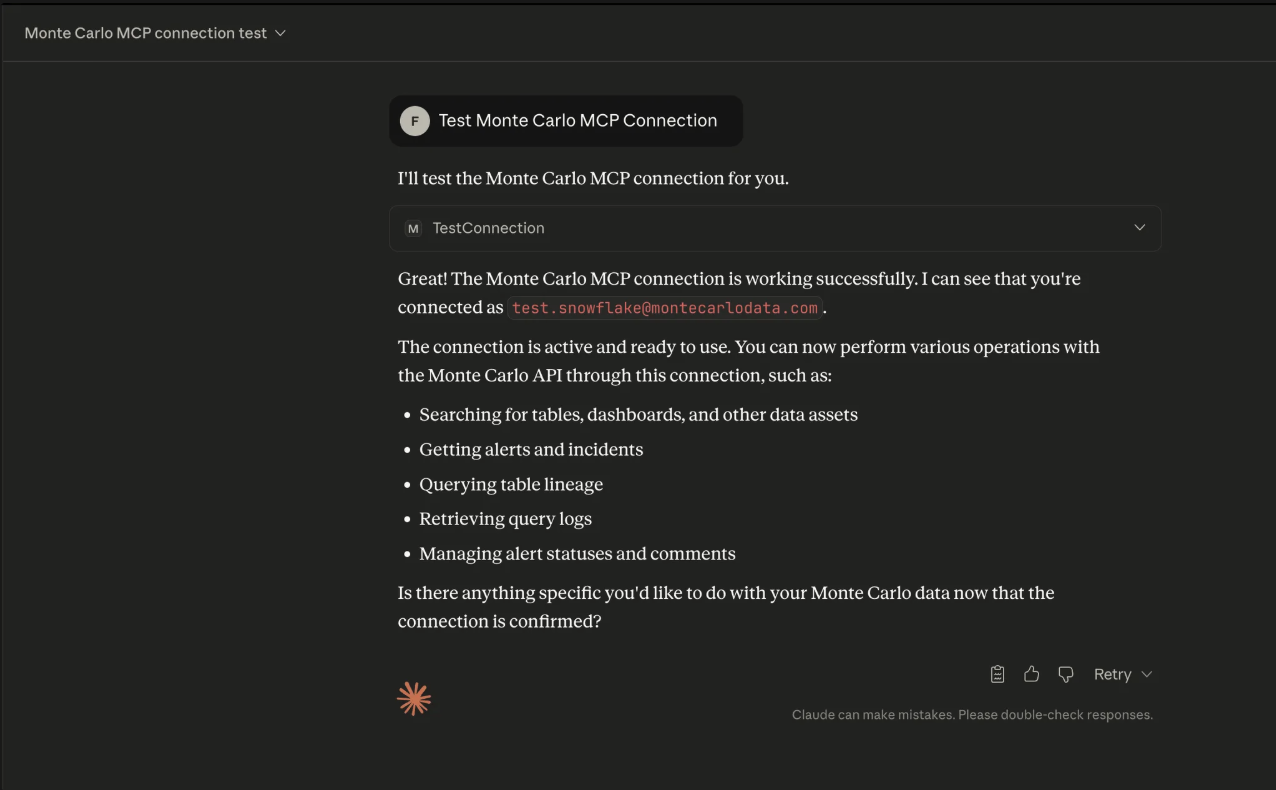
- Turn it on. Open an Agent Chat in Cursor and type:
Test Monte Carlo MCP connection. You should see it call thetest_connectiontool.
Setup in Visual Studio Code
- Open “Show and Run Commands” (SHIFT+CMD+P in Mac or SHIFT+Ctrl+P in Windows)
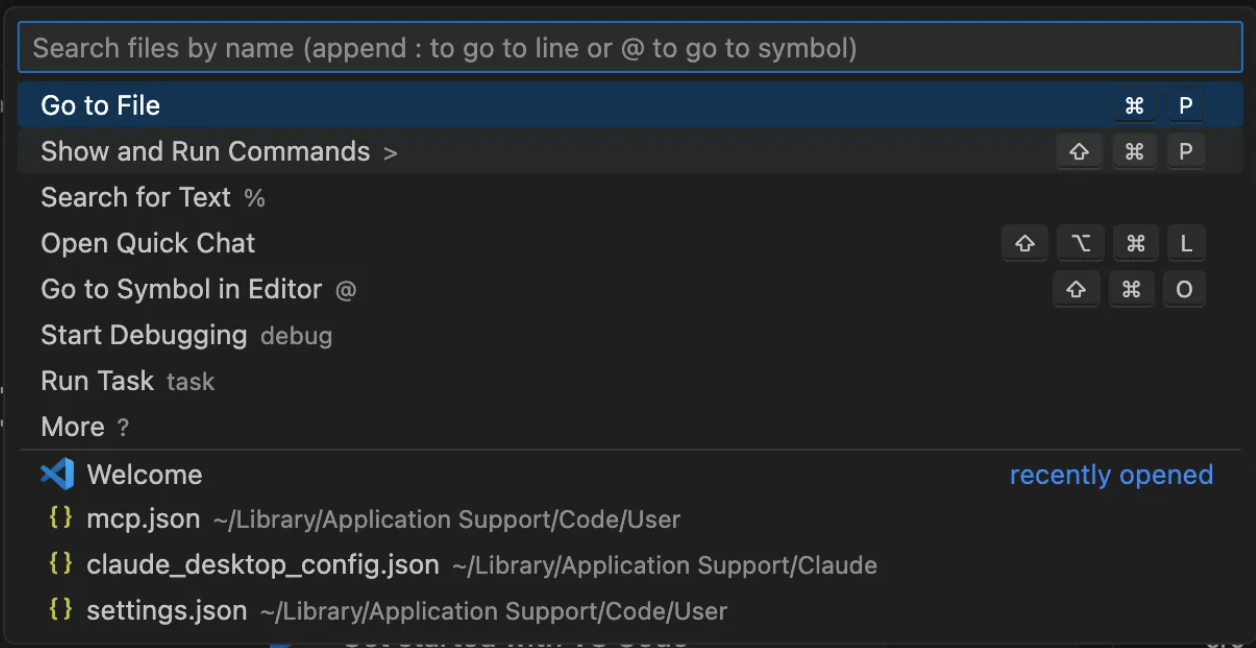
- Type “MCP: Open User Configuration”
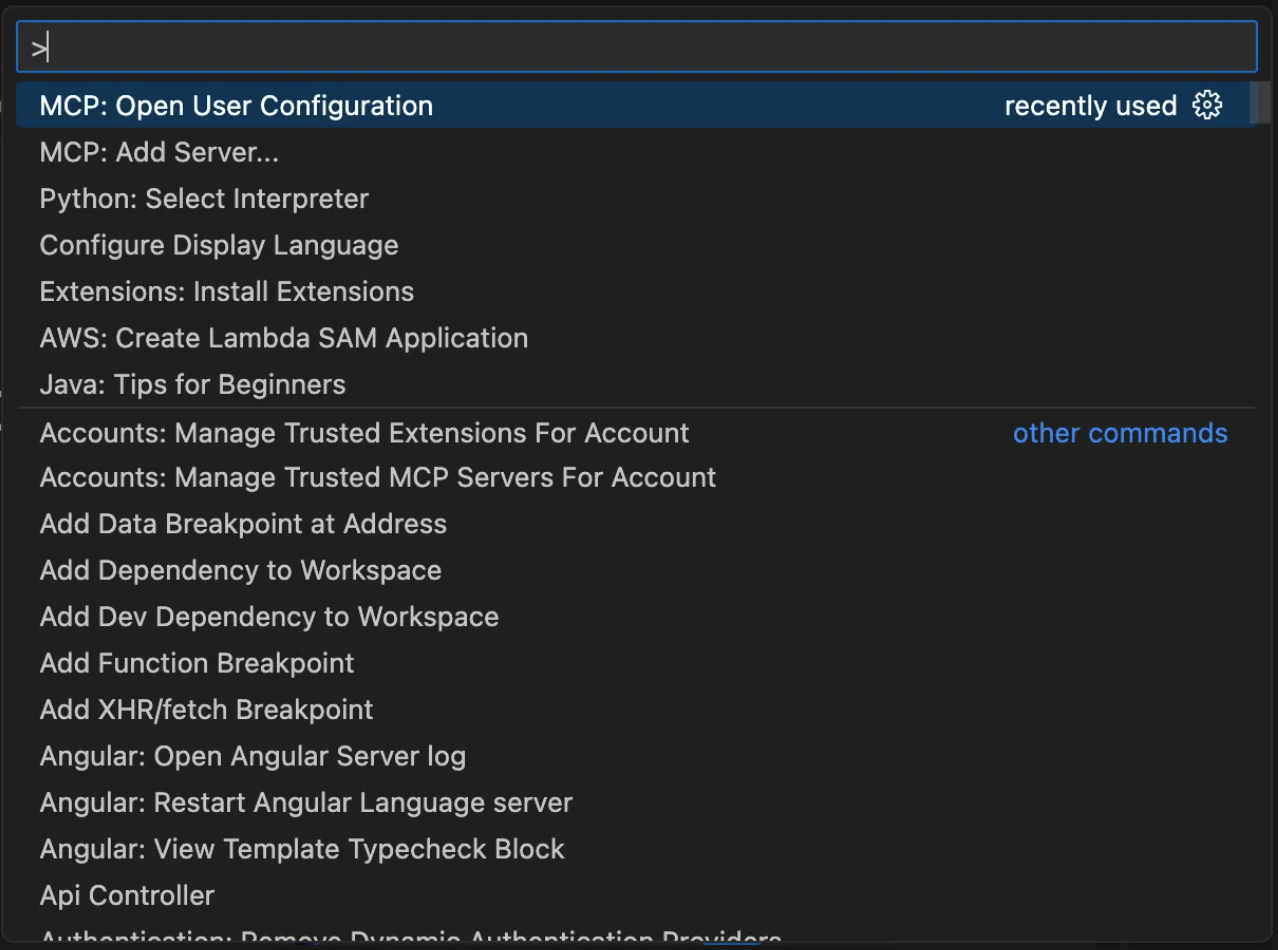
- This will open the
mcp.jsonfile, which should look something like this:
{
"servers": {}
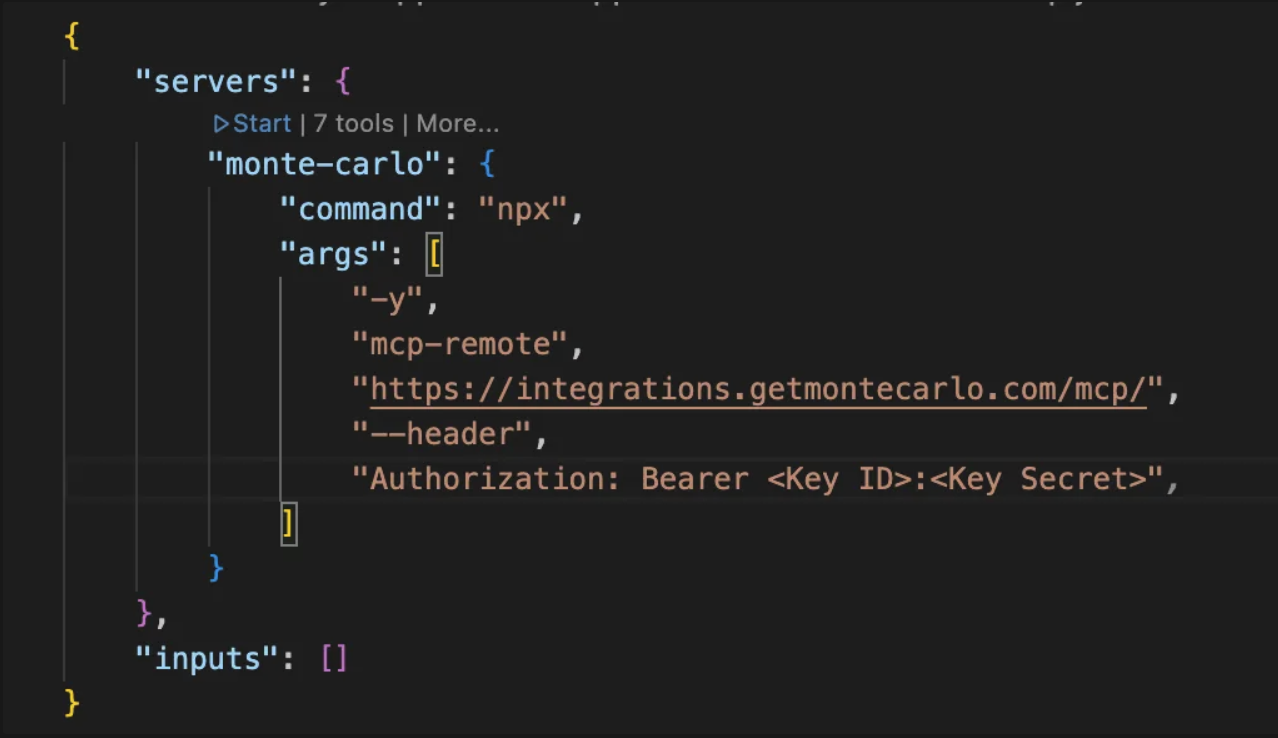
}- Add the Monte Carlo entry inside
servers(replace<KEY_ID>and<KEY_SECRET>with your values obtained from previous step.
{
"servers": {
"monte-carlo": {
"command": "npx",
"args": [
"-y",
"mcp-remote",
"https://mcp.getmontecarlo.com/mcp/",
"--header",
"Authorization: Bearer <KEY_ID>:<KEY_SECRET>"
]
}
},
"inputs": []
}Alternatively, we also support using custom headers instead of Authorization, so you can use the following:
{
"servers": {
"monte-carlo": {
"command": "npx",
"args": [
"-y",
"mcp-remote",
"https://mcp.getmontecarlo.com/mcp/",
"--header",
"x-mcd-id: <KEY_ID>",
"--header",
"x-mcd-token: <KEY_SECRET>"
]
}
},
"inputs": []
}- Save
mcp.jsonand click on the “Start” button over the “monte-carlo” MCP Server configuration
- Now the MCP Server should turn to “Running”:
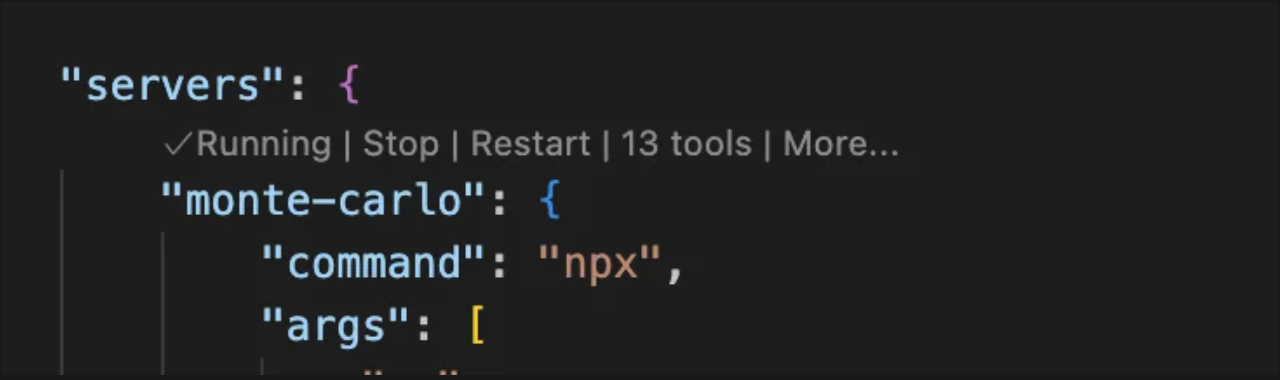
- Open the Chat screen and make sure the “Agent” mode is selected.
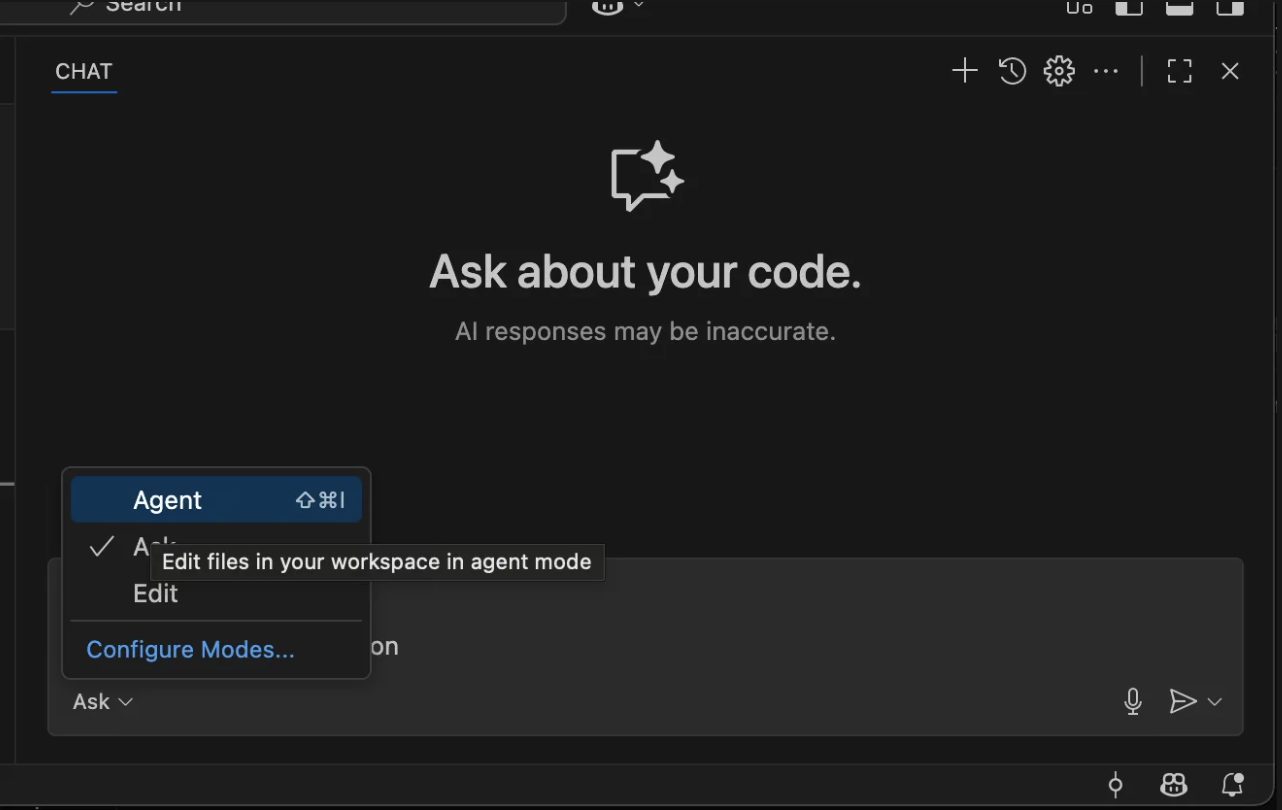
- Type:
Test Monte Carlo MCP connection. You should see it call thetest_connectiontool.
Setup in Claude Desktop
- Open Claude → Settings.
- Select Developer.
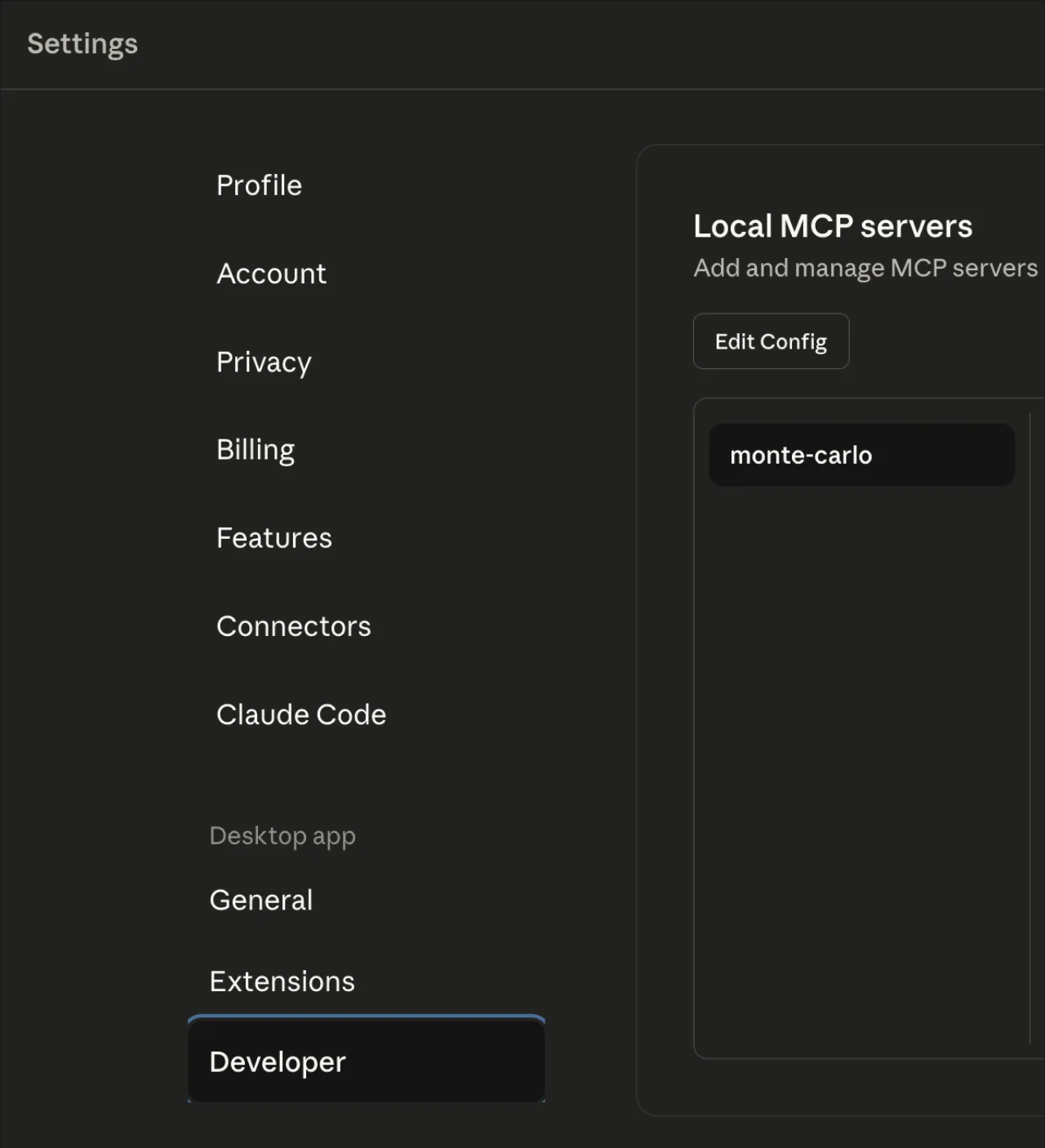
- Click the Edit Config button. This will open the location of the
claude_desktop_config.json. Open it in your preferred editor, you should see something like this:
{
"mcpServers": {
}
}- Add the Monte Carlo entry inside
mcpServers(replace<KEY_ID>and<KEY_SECRET>with your values obtained from previous step;
{
"mcpServers": {
"monte-carlo": {
"command": "npx",
"args": [
"-y",
"mcp-remote",
"https://mcp.getmontecarlo.com/mcp/",
"--header",
"Authorization: Bearer <Key Id>:<Key Secret>"
]
}
}
}Alternatively, we can also support using custom headers instead of Authorization:
{
"mcpServers": {
"monte-carlo": {
"command": "npx",
"args": [
"-y",
"mcp-remote",
"https://mcp.getmontecarlo.com/mcp/",
"--header",
"x-mcd-id: <KEY_ID>",
"--header",
"x-mcd-token: <KEY_SECRET>"
]
}
}
}- Save
claude_desktop_config.jsonand close Claude. Open it again and return to Settings → Developer. You should see a monte-carlo MCP Server in status Running.
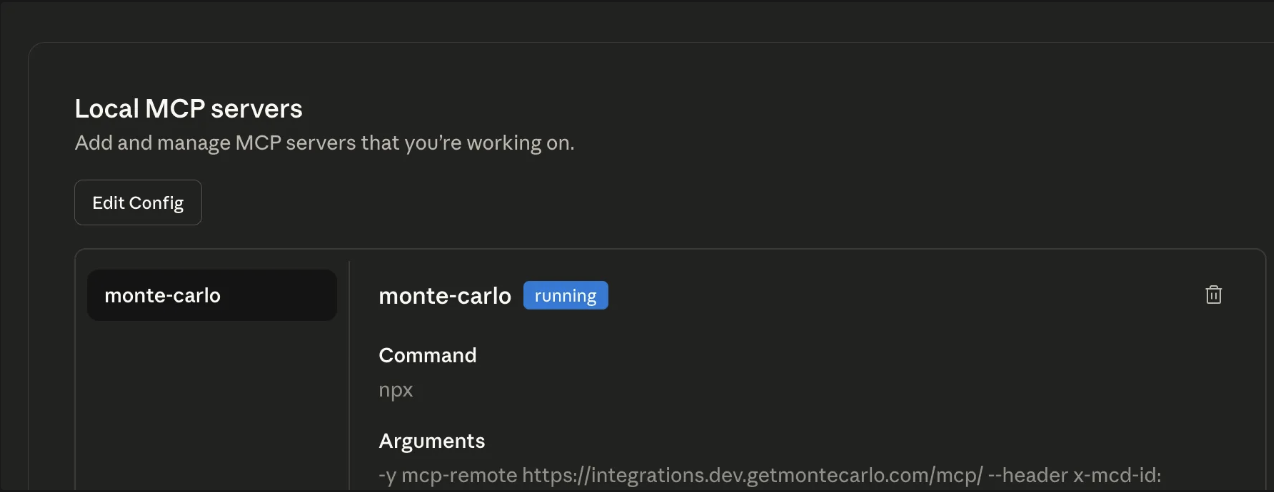
- Go to New Chat and type:
Test Monte Carlo MCP connection. You should see it call thetest_connectiontool.
Go further with the Agent Toolkit
The MCP Server connects your AI agent to Monte Carlo. The Agent Toolkit teaches it best practices — like checking data health before querying, monitoring your assets or analyzing schema changes for downstream impact. The toolkit includes skills and plugins for Claude Code and Cursor that build on top of the MCP Server.
Network Access Control
You can restrict access to the MCP Server endpoint by IP address using Network Access Control Lists. See Network Access Control for setup and configuration details.
Troubleshooting
- Toggle won't turn on / shows error
- Verify the URL (prod vs dev) and that it ends with
/mcp/. - Ensure
npxis available on your PATH; theyflag auto-installsmcp-remoteif missing.
- Verify the URL (prod vs dev) and that it ends with
- 401 / Unauthorized
- Double-check you pasted the correct Key id and Key secret.
- Check that you are passing the headers correctly(
Authorization: Bearer <id>:<secret>orx-mcd-id/x-mcd-token). - Make sure the key scope is MCP (API keys won’t work).
- Connection error: ServerError: HTTP 403: Invalid OAuth error response
- This error often occurs when using an outdated version of Cursor. Upgrade to the latest version.
- In some cases, the MCP Server output console will show missing parameters (e.g.,
Using custom headers: {"Authorization":""}). - This means the Authorization token is not being passed. Older versions of Cursor may incorrectly omit these headers.
- Network / proxy issues
- Confirm your corporate proxy allows requests to the MCP endpoint.
- Try again on a different network to rule out blocking.
- Cursor isn’t picking up changes
- Reopen Settings → MCP & Integrations or restart Cursor to reload
mcp.json.
- Reopen Settings → MCP & Integrations or restart Cursor to reload
Check and install Node.js + npm
Quick check
node -v && npm -v && npx -v
# Optional: verify the shim can run
npx -y mcp-remote --versionInstall tips
- macOS:
brew install nodeor (recommended)nvm install --lts - Linux:
curl -fsSL https://raw.githubusercontent.com/nvm-sh/nvm/v0.39.7/install.sh | bash && nvm install --lts - Windows:
winget install OpenJS.NodeJS.LTS
If you’re behind a proxy/allow-list, permit access to:
mcp.getmontecarlo.comregistry.npmjs.org(first run ofnpxfetchesmcp-remote)
One-liner sanity checks for MCP Server connection with curl
curlThese checks simply verify that auth headers are accepted by your endpoint. You’re good if you do not get 401/403. (Seeing 202 is fine for this quick test.)
macOS/Linux (bash/zsh)
export MCD_URL="https://mcp.getmontecarlo.com/mcp/"
export MCD_ID="<KEY_ID>"
export MCD_SECRET="<KEY_SECRET>"
# Authorization: Bearer <id>:<secret>
curl -sS -o /dev/null -w "%{http_code}\n" -X POST "$MCD_URL" \
-H "Authorization: Bearer $MCD_ID:$MCD_SECRET"
# OR alternate custom headers
curl -sS -o /dev/null -w "%{http_code}\n" -X POST "$MCD_URL" \
-H "x-mcd-id: $MCD_ID" \
-H "x-mcd-token: $MCD_SECRET"Windows PowerShell
$MCD_URL = "https://mcp.getmontecarlo.com/mcp/"
$MCD_ID = "<KEY_ID>"
$MCD_SECRET = "<KEY_SECRET>"
# Authorization: Bearer <id>:<secret>
(Invoke-WebRequest -Method POST $MCD_URL -Headers @{ Authorization = "Bearer $MCD_ID:$MCD_SECRET" } -UseBasicParsing).StatusCode
# OR alternate custom headers
(Invoke-WebRequest -Method POST $MCD_URL -Headers @{ "x-mcd-id" = $MCD_ID; "x-mcd-token" = $MCD_SECRET } -UseBasicParsing).StatusCodeAvailable Use-cases and Tools
- APIs to help users understand alerts: get_alerts
- APIs to help users manipulate alerts: update_alert, set_alert_owner, create_or_update_alert_comment
- APIs to answer questions about assets: search, get_table, get_queries_for_table, get_query_data
- APIs to understand asset dependencies: get_asset_lineage, get_downstream_bi_reports
- APIs to understand monitors: get_monitors, get_audiences
- APIs to create monitors as code: create_validation_monitor_mac, create_metric_monitor_mac, create_comparison_monitor_mac, create_custom_sql_monitor_mac, create_table_monitor_mac
- APIs to explore use cases: get_use_cases, get_use_case_table_summary, get_use_case_tables
- APIs to observe AI agents: get_agent_metadata, get_agent_conversation, get_agent_trace
- API to create dashboard widgets: create_custom_dashboard_widget
- Other APIs to ensure smooth interaction with the MCP server: test_connection, get_domains, get_user, get_current_time, get_validation_predicates
Users can leverage it to ask questions such as:
- "Are there any alerts assigned to me in the past day?"
- "How's the health status of table X?"
- "What are some trends and patterns in my alerts?"
- "What tables should I add monitors for?"
- "When was my table Y last updated?"
- "What assets and reports would this data issue impact?"
- "What BI dashboards depend on this table?"
- "What are the most critical tables in this use case?"
- "What AI agents are available and how are they performing?"
- "Can I deprecate table X?", and many more.
| Category | Tool Name | Description | Example Use Cases |
|---|---|---|---|
| Alerts | get_alerts | Retrieve alerts and incidents from Monte Carlo with filtering options | • Get recent data quality alerts for a specific time period • Filter alerts by severity, status, or data assets • Generate reports on incident trends and patterns |
| Alerts | update_alert | Update alert status, severity, or metadata | • Mark alerts as acknowledged or resolved • Declare incidents by setting severity levels • Add custom names to alerts for tracking |
| Alerts | set_alert_owner | Assign or remove alert ownership | • Assign alerts to team members for investigation • Clear ownership when transferring responsibility • Manage alert assignment workflows |
| Alerts | create_or_update_alert_comment | Add comments to alerts for collaboration | • Document investigation findings and next steps • Share context with team members on alert resolution • Track alert resolution progress and decisions |
| Monitors | get_monitors | Get monitors from Monte Carlo based on specified filters | • List monitors for a specific table or domain • Review monitor configurations and metadata • Audit monitoring coverage across assets |
| Monitors | get_audiences | Get notification audiences from Monte Carlo | • View configured notification routing • Understand who gets notified about data quality issues • Review audience groupings for monitors |
| Monitors | create_validation_monitor_mac | Generate YAML configuration for validation monitors (monitors as code) | • Create data quality rules using monitors-as-code • Define custom validation logic for specific tables • Automate monitor deployment through CI/CD pipelines |
| Monitors | create_metric_monitor_mac | Generate YAML configuration for metric monitors (monitors as code) | • Track metric trends over time • Set up threshold-based monitoring • Automate metric monitor deployment |
| Monitors | create_comparison_monitor_mac | Generate YAML configuration for comparison monitors (monitors as code) | • Compare data across tables or time periods • Detect drift between datasets • Automate comparison monitor deployment |
| Monitors | create_custom_sql_monitor_mac | Generate YAML configuration for custom SQL monitors (monitors as code) | • Define custom SQL-based data quality checks • Create monitors with complex business logic • Automate custom SQL monitor deployment |
| Monitors | create_table_monitor_mac | Generate YAML configuration for table monitors covering groups of tables (monitors as code) | • Set up freshness, volume, and schema monitoring for entire databases or schemas • Automate table-level monitor deployment • Monitor groups of tables with asset selection rules |
| Monitors | get_validation_predicates | List available predicates for creating validation monitors | • Discover supported validation rule types • Understand predicate syntax and parameters • Build complex validation conditions |
| Data operations | get_queries_for_table | Retrieve query logs for a table, showing reads or writes over time | • Analyze table usage patterns and frequency • Identify which queries are updating specific tables • Investigate data lineage through query analysis |
| Data operations | get_query_data | Get full query text and metadata for specific query occurrences | • Review complete SQL for truncated query snippets • Analyze query performance and execution details • Debug data pipeline issues |
| Assets/Catalog | get_table | Get detailed table information including schema, statistics, and metadata | • Understand table structure and data types • Review table statistics and monitoring capabilities • Explore table metadata and tags |
| Assets/Catalog | search | Search the Monte Carlo catalog for tables, views, dashboards, and other assets | • Find tables by name or description across warehouses • Discover related data assets and BI reports • Locate specific datasets within large data catalogs |
| Assets/Catalog | get_domains | List available domains in your Monte Carlo workspace | • Understand data organization and ownership • Filter other operations by domain • Navigate domain-based access controls |
| Dependencies | get_asset_lineage | Trace upstream and downstream data flow relationships | • Map data flow between tables and systems • Understand impact analysis for schema changes • Visualize end-to-end data pipelines |
| Dependencies | get_downstream_bi_reports | Find all downstream BI assets (Tableau, Looker, Power BI, etc.) that depend on given source tables | • Identify BI dashboards impacted by a data issue • Assess blast radius of schema changes • Map table-to-report dependencies |
| Agent Observability | get_agent_metadata | List AI agents with their names, trace table MCONs, and source types | • Discover available AI agents in the account • Get agent identifiers needed for conversation and trace lookups • Review agent inventory |
| Agent Observability | get_agent_conversation | Get the ordered thread of LLM spans (prompts and completions) for a specific AI agent conversation | • Inspect a conversation's full prompt/completion exchange • Debug agent behavior by reviewing the sequence of LLM interactions • Analyze token usage and latency |
| Agent Observability | get_agent_trace | Get the full span tree for a specific AI agent trace | • Inspect the detailed execution flow of an agent trace • Reconstruct the parent/child span hierarchy • Analyze span durations and identify bottlenecks |
| Use cases | get_use_cases | Get all use cases for a warehouse, representing business-critical data flows | • Discover monitoring opportunities for data products • Review use case criticality levels • Understand business-critical data flows |
| Use cases | get_use_case_table_summary | Get table criticality counts for a specific use case | • Assess monitoring coverage by criticality level • Prioritize tables for monitoring • Understand distribution of critical assets |
| Use cases | get_use_case_tables | Get tables associated with a use case, with criticality levels and golden table status | • Identify the most business-critical tables • Review table criticality reasoning • Find golden tables in a use case |
| Dashboards | create_custom_dashboard_widget | Generate validated widget JSON for Monte Carlo custom dashboards | • Create charts, graphs, and tables for dashboards • Visualize data quality metrics • Build custom monitoring dashboards |
| Other | test_connection | Verifies connectivity and authentication with the Monte Carlo API | • Test MCP setup during initial configuration • Validate credentials and network connectivity • Troubleshoot connection issues |
| Other | get_user | Get current user information and permissions | • Verify authentication and user context • Check user permissions and access levels • Validate user-specific configurations |
| Other | get_current_time | Get current time in ISO format for API compatibility | • Generate time ranges for other API calls • Ensure consistent timestamp formatting • Calculate relative time periods |
Toolsets
Not all tools are available in every deployment. The MCP server organizes tools into toolsets that control which tools are exposed to the client:
| Toolset | Description | Tools included |
|---|---|---|
| default | Standard tools available in all deployments. Covers alerts, monitors, assets, lineage, data operations, and utility tools. | All tools except those listed in Extended and Agent Observability |
| extended | Includes all default tools plus additional tools for use cases and dashboard widgets. | Default tools + get_use_cases, get_use_case_table_summary, get_use_case_tables, create_custom_dashboard_widget |
| agent_observability | Includes all default tools plus tools for inspecting AI agent conversations and traces. | Default tools + get_agent_metadata, get_agent_conversation, get_agent_trace |
The default toolset is always active. To enable extended or agent_observability, pass the x-mcd-toolset HTTP header when connecting to the MCP server. With the key-based (npx mcp-remote) setup, add an extra --header argument to your client configuration:
"--header",
"x-mcd-toolset: extended"Valid values are extended and agent_observability.
See a quick demo below on the MCP server in action:
Updated 16 days ago
