Generic Agent Deployment (Public Preview)
This is a more advanced deployment. If you want to use an agent, Monte Carlo generally recommends the cloud-native options for AWS, Azure or GCP.
This deployment is currently in preview. All relevant documentation is self-contained within this page and its children. The networking and architecture guides for other deployment types do not apply.
Because hosting environments vary widely, these docs provide simplified reference examples. Your deployment may require additional configuration for networking, security, and infrastructure based on your organization's requirements. Hosting, monitoring, and maintaining (e.g., upgrading) the agent is part of your shared responsibility.
This feature requires an Enterprise plan or a plan with Advanced Networking.
This guide outlines how to deploy and register a Generic Agent. The Generic Agent runs on any platform that supports Docker — including AWS, Azure, GCP, other cloud providers, and on-premises infrastructure. All connections are initiated outbound from the agent to Monte Carlo; no inbound ports need to be opened, and credentials remain on your infrastructure.
The FAQs answer common questions like how to review resources and what integrations are supported.
Architecture
The Generic Agent uses an egress-only architecture — all network connections are initiated from the agent to the Monte Carlo platform. No inbound connectivity to the agent is required, and no ports need to be exposed.
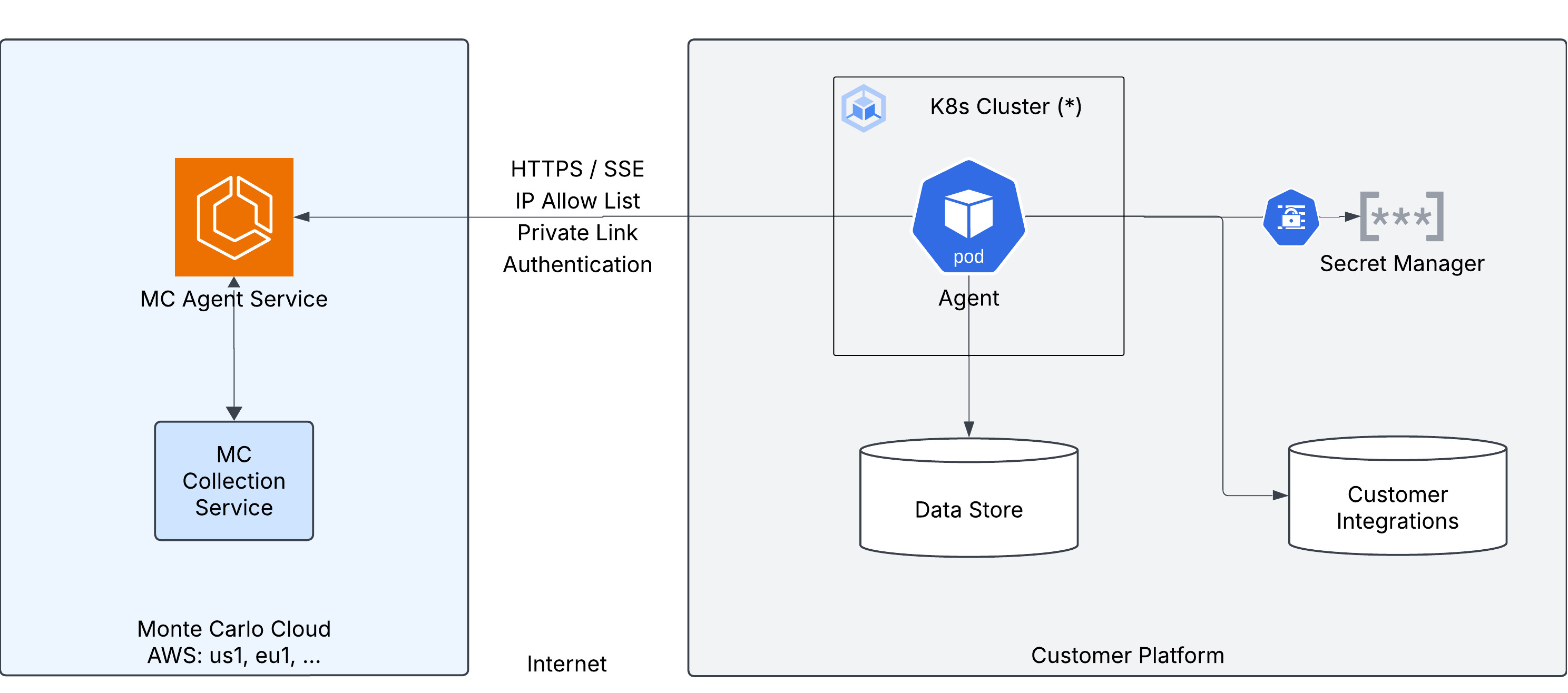
The agent connects to the MC Agent Service via HTTPS using Server-Sent Events (SSE) to open a persistent stream and receive operations to execute. Polling is also used as a fallback. Results are pushed back over HTTPS. The MC Agent Service forwards the results to the MC Collection Service for processing.
On the customer side, the agent runs inside a Kubernetes cluster (or any environment capable of running Docker containers) and connects to:
- Data Store — object storage (S3, GCS, Azure Blob, or S3-compatible) for sampling and any temporary data during operations. This storage is private and accessed only through the agent.
- Secret Manager — stores the agent token and integration credentials. The specific service depends on the platform: AWS Secrets Manager, Azure Key Vault, GCP Secret Manager, or Kubernetes Secrets.
- Customer Integrations — the data sources being monitored by Monte Carlo.
Key characteristics:
- Egress-only — the agent initiates all connections; no inbound firewall rules are needed.
- Authentication — the agent supports two authentication methods, chosen during registration: Key/Token (a Monte Carlo-generated key pair) or OAuth (OAuth 2.0 Client Credentials with automatic JWT token management). See Authentication below.
- IP Allow List — optionally configure in Monte Carlo the list of IP addresses allowed to connect on behalf of the agent. The MC Agent Service also uses static IP addresses that customers can add to their outbound allow lists.
- Private Link — optionally route traffic over AWS PrivateLink or Azure Private Link instead of the public internet.
- Proxies and Traffic Inspection — optionally route agent traffic through a proxy.
- Runs anywhere — any infrastructure that can run a Docker container can host the agent: cloud-managed Kubernetes (EKS, AKS, GKE), self-managed Kubernetes, or Docker Compose on any host with Docker installed.
Authentication
The Generic Agent supports two authentication methods. The method is chosen during agent registration and cannot be changed afterward.
Key/Token (Default)
The agent authenticates using a Monte Carlo-generated key pair — a Key ID (mcd_id) and Key Secret (mcd_token). These credentials are passed to the agent as a JSON file and sent as headers on every request to the Monte Carlo Agent Service.
This is the simplest option and works well for most deployments.
OAuth (Client Credentials)
The agent authenticates using the OAuth 2.0 Client Credentials flow. During registration, you receive a Client ID and Client Secret. The agent uses these to automatically obtain a short-lived JWT access token from Monte Carlo's token endpoint, and includes the token as a Bearer header on every request to the Agent Service.
Key characteristics:
- Automatic token management — the agent obtains and refreshes tokens automatically. No manual token handling is required.
- Short-lived tokens — access tokens expire after 1 hour by default, limiting the window of exposure if a token is intercepted.
- Standard protocol — uses the industry-standard OAuth 2.0 Client Credentials flow, which may align better with organizations that have existing OAuth infrastructure, audit requirements, or policies that mandate token-based authentication.
- Credential rotation — to rotate credentials, generate a new OAuth client from the agent's settings page in Monte Carlo, update the secret on your infrastructure, and delete the old client. Already-issued tokens remain valid until they expire.
Supported Platforms
| Platform | Guide | Best for |
|---|---|---|
| Docker Compose | Generic Agent: Docker Compose Deployment | Quick setup on a single host — ideal for evaluation, development, and small deployments without Kubernetes. |
| Kubernetes | Generic Agent: Kubernetes Deployment | Any existing Kubernetes cluster, on-premises deployments, or environments where you manage infrastructure with Helm and kubectl directly. |
| AWS (EKS) | Generic Agent: AWS EKS Deployment | AWS deployments using Terraform. Provisions VPC, EKS cluster, S3 storage, Secrets Manager, and IAM automatically. |
| Azure (AKS) | Generic Agent: Azure AKS Deployment | Azure deployments using Terraform. Provisions VNet, AKS cluster, Blob Storage, Key Vault, and managed identity automatically. |
| GCP (GKE) | Generic Agent: GCP GKE Deployment | GCP deployments using Terraform. Provisions VPC, GKE cluster, GCS storage, Secret Manager, and IAM automatically. |
Secrets Management
For details on how the agent accesses secrets — including using Kubernetes Secrets directly or cloud secret managers (AWS Secrets Manager, Azure Key Vault, GCP Secret Manager) via External Secrets Operator — see the Secrets Management guide.
Networking
Outbound Destinations
The agent is egress-only — no inbound connectivity is required. It initiates connections to:
| Destination | Purpose | Port |
|---|---|---|
Monte Carlo Agent Service — e.g. artemis.getmontecarlo.com (or your PrivateLink endpoint) | SSE stream + operation results | 443 |
Monte Carlo Token Endpoint — e.g. m2m.getmontecarlo.com (OAuth only) | OAuth 2.0 token acquisition and refresh | 443 |
| Object storage — your S3 bucket / Azure Blob container / GCS bucket / S3-compatible endpoint | Data Sampling and temporary operation data | 443 |
| Secret store — AWS Secrets Manager / Azure Key Vault / GCP Secret Manager | Token + integration credentials | 443 |
| Customer integrations — your data sources (Snowflake, Redshift, BigQuery, etc.) | Operation execution against integrations | typically 443, integration-specific |
| Container registry — Docker Hub or your image mirror | Image pulls (handled by the cluster, not the agent process) | 443 |
The exact Monte Carlo backend hostname is region-dependent and shown on your account's Account Information page under Agent Service.
Any of these connections can be routed through a forward proxy or a TLS-inspecting firewall — see Proxies and Traffic Inspection.
Private Connectivity
If your organization requires that no traffic traverses the internet between the agent and Monte Carlo Agent Service, use Private Link
| Platform | Guide |
|---|---|
| AWS | Agent Service AWS PrivateLink |
| Azure | Agent Service Azure Private Link |
| On-Premises | On-Premises Private Connectivity |
Proxies and Traffic Inspection
You may want to route agent traffic through a corporate proxy or inspect the data sent by the agent to Monte Carlo. See the Proxies and Traffic Inspection guide for a detailed overview of all options.
| Scenario | Platform | Guide |
|---|---|---|
| Forward Proxy | Kubernetes | How do I route agent traffic through a forward proxy? |
| Forward Proxy | Docker Compose | How do I route agent traffic through a forward proxy? |
| TLS Inspection | Kubernetes | How do I inspect HTTPS traffic from the agent? |
| TLS Inspection | Docker Compose | How do I inspect HTTPS traffic from the agent? |
IP Allow List
You can configure which IP addresses are allowed to connect to the Agent Service on behalf of your agent. When configured, only requests from IP addresses in the allowlist will be accepted. This is configured using the Network Access Control feature with the Agent scope.
Static IP Addresses (Outbound)
The Agent Service uses static IP addresses that you can add to your outbound allow lists (e.g. firewall rules). These addresses are available in the Account Information page in Monte Carlo, under Agent Service > Public IP addresses.
FAQs
What is the data store used for?
The data store (S3, GCS, Azure Blob Storage, or S3-compatible) is used by the agent to store data samples and temporary data during operations. Data samples are limited sets of rows retrieved from your warehouse that provide richer context during investigation and alert triage — such as root cause analysis (RCA) and breached row inspection. This storage is private and accessed only through the agent. See the Configuring Data Sampling documentation for more details on how sampling works and how to control it.
What integrations are supported?
The Generic Agent supports all integrations that work with Self-Hosted Credentials. See that page for the full list of supported integration types and how to configure them.
Can I review the agent source code and resources?
Yes. The source code for the Generic Agent is available at monte-carlo-data/hermes-agent on GitHub.
Updated 1 day ago
